Improving your digital presence is an adventure. Let us guide you through it.
Contact us using the form below and one of our team members will reach out as soon as possible.
(*) - Required field

After having several of our clients victimized by real-life phishing scams, we've gathered the resources you need to keep yourself protected.
Businesses of all sizes can be victimized by phishing attacks. That’s because no matter where you are, what you sell, or who your clients are, everyone holds some amount of valuable digital information. Bad actors are eager to get their hands on that data, and phishing is one tried-and-true way they can do this.
A play on the age-old pastime (and pronounced the same way, too) phishing uses the same tactics: lures, bait, and disguised identity. Cyber criminals could use seemingly legit email messages to get your employees to click on malicious links or attachments. Victims are then taken to a fake site where they can enter information and give these bad actors the keys to your data vault.
While it’s terribly sneaky of them, you’ve got to admit that it’s much simpler for cyber criminals to be invited inside than it is to scale digital walls and barriers. This is precisely why attackers so often use phishing scams, and why you need to be on the offensive.
A “successful” phishing attack can yield login credentials, account information, payment details, and plenty of other sensitive data that can put your company and clients in jeopardy.
Speak with one our team members
At a quick glance, phishing communications can seem to be legitimate. But with just a bit of scrutiny, you can be more confident in your evaluation and avoid criminal attacks. Here’s what to look for:
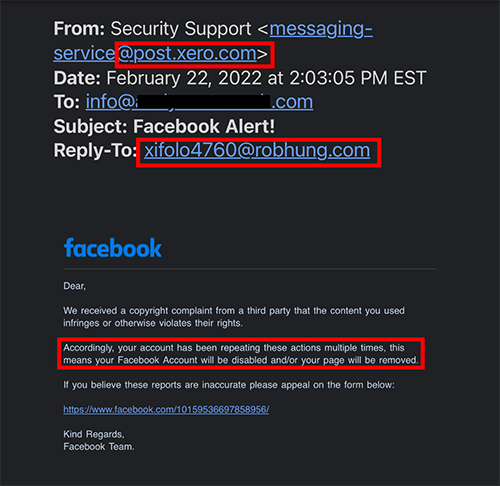
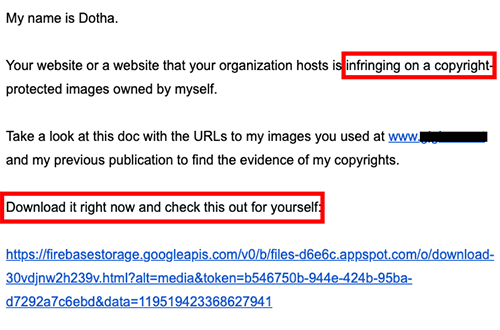
All of these factors combine to create a situation that feels uneasy and can generate a false sense of urgency––that’s their goal. Cyber criminals are hoping that in the confusion, you share information you normally wouldn’t.
When it comes to phishing scams, prevention is the best medicine, and in this case education and awareness factor heavily if you’re trying to make your company phishing-resistant. Sharing expert tips and information on how to recognize and avoid phishing can go far to prepare your staff to view every email with a more critical eye. To that end, here’s a great video and article that we’ve vetted for you.
Email phishing attacks are probably the oldest and most common type of phishing you can expect to encounter. But there are other tactics to be aware of. Here are some of the most widespread types of phishing to know:
Oftentimes the platform your company uses to manage emails can help to flag suspicious messages. If so, heed those warnings. Be sure to pay flagged emails extra attention and to be diligent in how you follow up.
You can also contact the supposed person or organization to inquire about the email, so long as you do so directly, and outside of the message in question.
There is no single fool-proof method to prevent phishing attacks. By keeping on guard and taking the time to scrutinize any message that appears suspicious, you can ward off the majority of attempts that land in your inbox.
At Alt Media Studios we’re here for your success. So we’re happy to share what we’ve learned from experience in the hopes that it will help you too. Stay tuned and keep in touch for more practical, helpful tips from our team. We’re wishing you the best.
What is an ideal blog posting schedule? Go ahead and enter that question into any search engine and the range of answers you’ll get is head-spinning. Four times a week, once a week, every day, once a month–what is the right answer?

The old proverbial slow-but-steady approach is the way to go. Here’s what the SEO experts at Alt Media Studios have to share about a realistic SEO timeline.

Once you know the time of year that typically brings in the most business for you, it’s vital to capitalize on that opportunity. We have advertising and digital marketing down to a science, and we’re here to share some key tips about timing.